A Leader in Cyber Securityand Policy Management
Protecting enterprises with advanced security
and comprehensive policy management
Trusted Enterprise Security Since 2000
Since 2000, we've licensed our technology to industry leaders including Microsoft, Citrix, NetIQ, LogMeIn, F5 Networks, OpenText and others. More than 5 million users and 1500 organizations rely on technology developed by Full Armor.
Whether on-premise or in the cloud, Full Armor helps Fortune 1000 companies secure and manage their IT resources.
Our Products
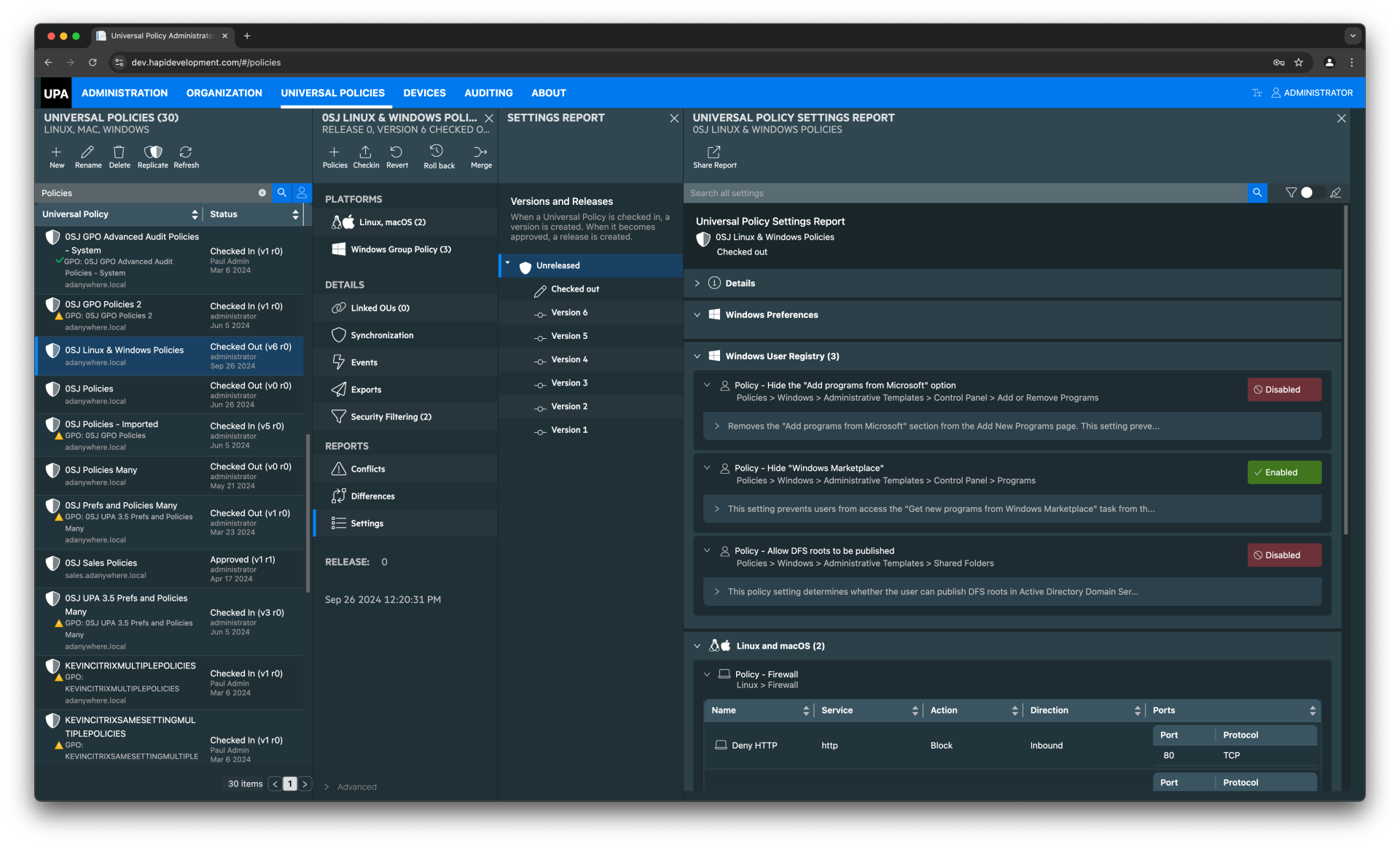
Universal Policy Administrator
Enterprise-grade Group Policy Management and Change Control solution for secure IT environments.
- Comprehensive policy management
- Change tracking and auditing
- Enterprise-wide deployment
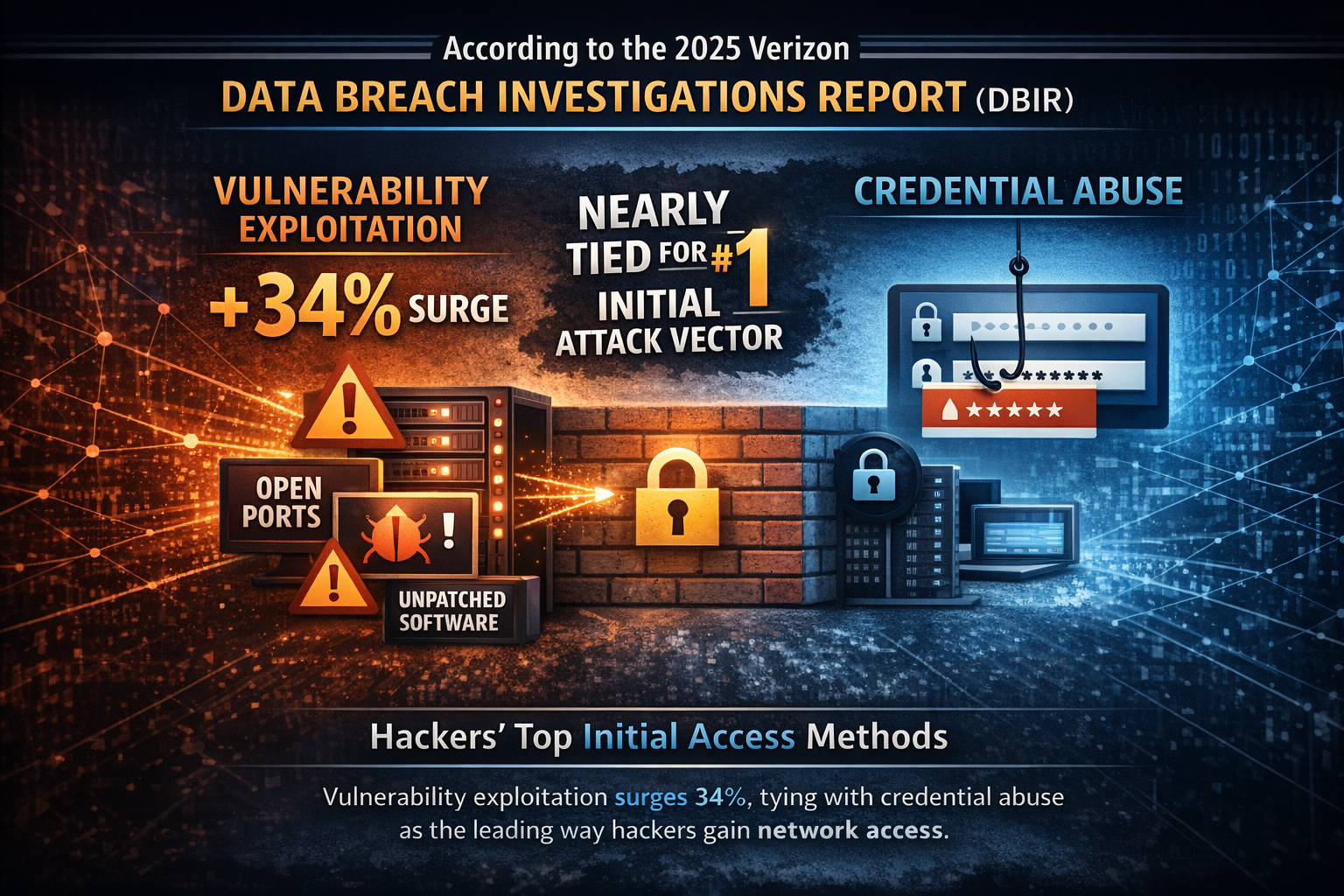
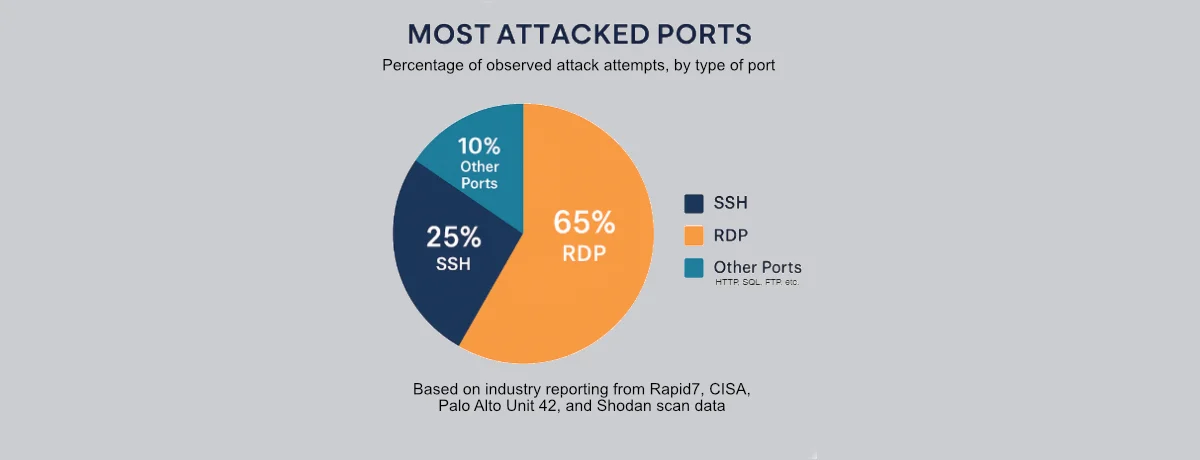
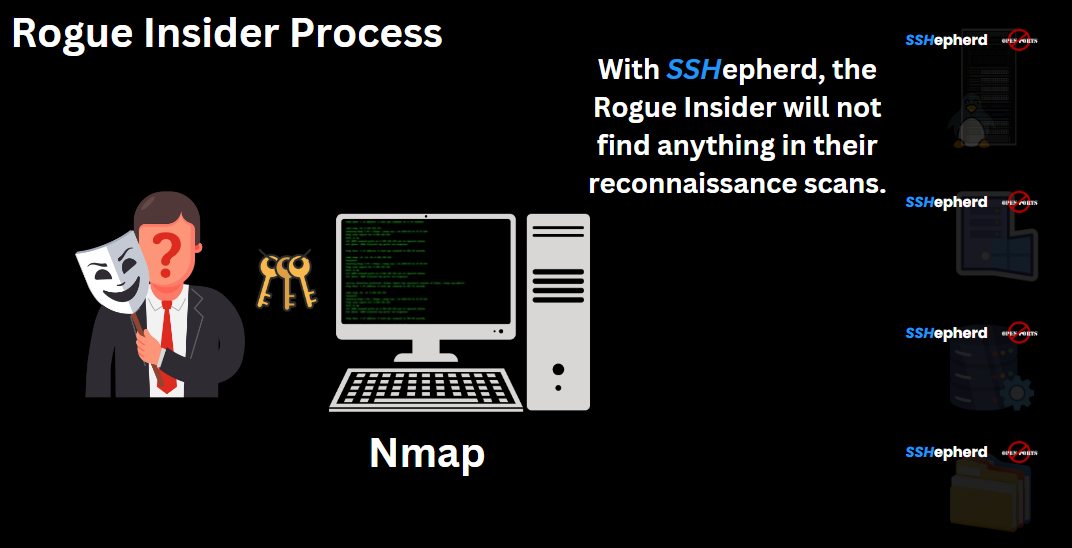
SSHepherd®
Advanced stealth cybersecurity for SSH, RDP, and Applications, ensuring secure remote access and management.
- SSH and RDP protection
- Application security
- Access control management
Contact Us
Please contact us to learn how Full Armor can help to protect your IT infrastructure.
Our team of security experts is ready to help you implement the right solutions for your enterprise.